Default values, documentation and Ansible
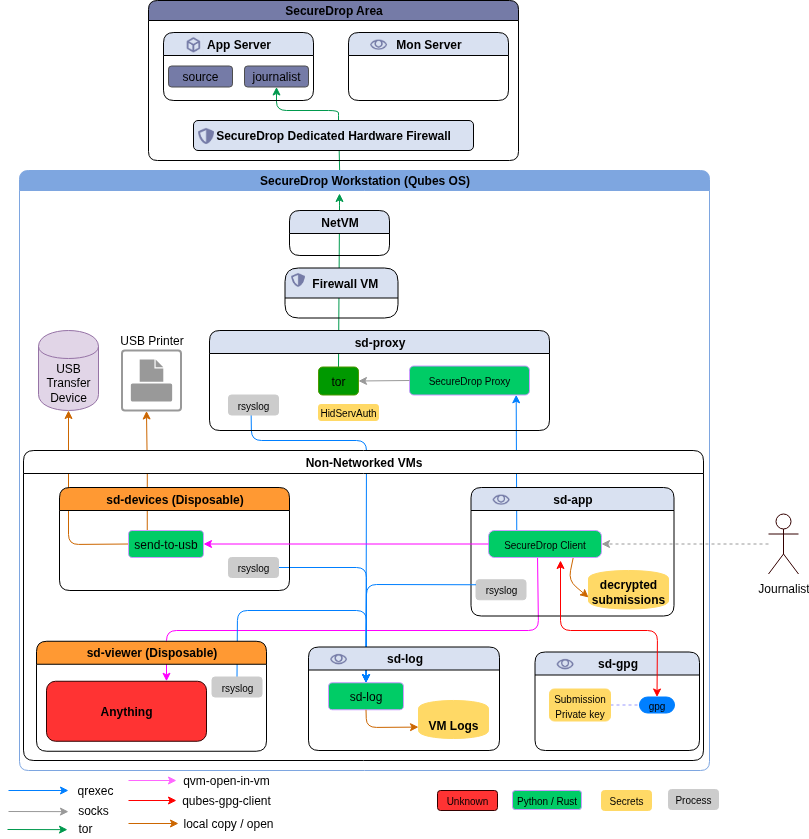
While testing my qubes_ansible project on the upcoming Qubes OS 4.1 project, I noticed something really strange. But, before getting into that, this Ansible module and the connection plugin are for Qubes OS only, and based on the excellent Python modules provided by the Qubes team.
The error goes like this during the fact gathering steps (reformatted for the blog):
fatal: [debian-10]: UNREACHABLE! => {
"changed": false,
"msg": "Failed to create temporary directory.In some cases, you may have
been able to authenticate and did not have permissions on the target
directory. Consider changing the remote tmp path in ansible.cfg to a path
rooted in \"/tmp\", for more error information use -vvv. Failed command
was: ( umask 77 && mkdir -p \"` echo ~The *user* is the default user in
Qubes./.ansible/tmp `\"&& mkdir \"` echo ~The *user* is the default user in
Qubes./.ansible/tmp/ansible-tmp-1630548982.9355698-7707-90110802425258 `\"
&& echo ansible-tmp-1630548982.9355698-7707-90110802425258=\"` echo ~The
*user* is the default user in
Qubes./.ansible/tmp/ansible-tmp-1630548982.9355698-7707-90110802425258 `\"
), exited with result 1, stderr output: mkdir: cannot create directory
‘~The ~The *user* account as default in Qubes OS. ~The ~The *user* account
as default in Qubes OS. account as default in Qubes OS. ~The ~The *user*
account as default in Qubes OS. ~The ~The *user* account as default in
Qubes OS. account as default in Qubes OS. account as default in Qubes OS.
is the default user in Qubes.’: File name too long\n",
"unreachable": true
}
Most important part is the default user's home directory part, echo ~The
user is the default user in Qubes./.ansible/tmp. For a moment I totally
freaked out, as this looks like documentation. After reading the code more, I
can see it is coming from the DOCUMENTATION variable in my plugin. After
playing around a bit more and trying out different values I can see that the
default value mentioned in the documentation is becoming the default value in
the Python code.
After searching more I can see that the Ansible developers want the documentation string to be the gold standard and the code is parsing it find the default values. In my mind this is more confusing. I would expect the default value to be declared inside of the code.
Parsing the DOCUMENTATION and then finding the default values there in a
Python code still does not fit in my brain. Fixed the issue for now, let me see
what other surprises are waiting in the future.