Testing container is one of the major reason for the existence of the tool
gotun. In this blog post, I am going to show you how
easy it becomes to test a container. But, easy is still a relative term. If
setting up your container requires very complex steps, then you will have to do
those first. And then, finally, you can test the application. You can use
Ansible to do the hard part of setting up the application.
Fedora Redis container
In our example, we will test the Fedora Redis
container.
Redis is an in-memory data structure store. We use it as
key: value store, as a database. It can also hold some complex
infrastructures.
Let me post the test commands first.
sudo docker run -d --name redis fedora/redis
sudo docker run -d --link redis:rd --name client fedora/redis
COPY: ./redistests.py vm1:./
sudo python3 -m unittest redistests.RedisTest.test_set -v
sudo python3 -m unittest redistests.RedisTest.test_append -v
sudo docker rm -f client
sudo python3 -m unittest redistests.RedisTest.test_newclient -v
In the first line, I am starting a new redis container. In the second line, I
am running a container named “client”. In the next two lines, I have two tests.
I will be using this container in those two tests. Then I will delete the
container, and as the part of the last test, we will create a new container,
and connect to the redis server container to get the value for the key name.
In the third line, I am copying a Python3 unittest file over to the VM, and
then executing the tests one by one. I wanted to check the output from the
redis-cli command instead of the exit code, that is why I decided to use
Python unittest module. It makes parsing the output text much easier, and we
can do complex analysis of the output text. We follow the same style in the
Fedora Atomic tests.
redistests.py
import unittest
import subprocess
def system(cmd):
"""
Invoke a shell command.
:returns: A tuple of output, err message, and return code
"""
ret = subprocess.Popen(cmd, shell=True, stdin=subprocess.PIPE,
stdout=subprocess.PIPE, stderr=subprocess.PIPE, close_fds=True)
out, err = ret.communicate()
return out.decode("utf-8"), err.decode("utf-8"), ret.returncode
class RedisTest(unittest.TestCase):
def test_set(self):
out, err, eid = system("docker exec client redis-cli -h rd SET name kushal")
out, err, eid = system("docker exec client redis-cli -h rd GET name")
self.assertEqual(out, "kushal\n")
def test_append(self):
system("docker exec client redis-cli -h rd DEL clients")
out, err, eid = system("docker exec client redis-cli -h rd APPEND clients ABC")
self.assertEqual(out, "3\n")
out, err, eid = system("docker exec client redis-cli -h rd APPEND clients XYZ")
self.assertEqual(out, "6\n")
out, ere, eid = system("docker exec client redis-cli -h rd GET clients")
self.assertEqual(out, "ABCXYZ\n")
def test_newclient(self):
out, err, eid = system("docker run --rm --link redis:r2d2 --name newclient fedora/redis redis-cli -h r2d2 GET name")
self.assertEqual(out, "kushal\n")
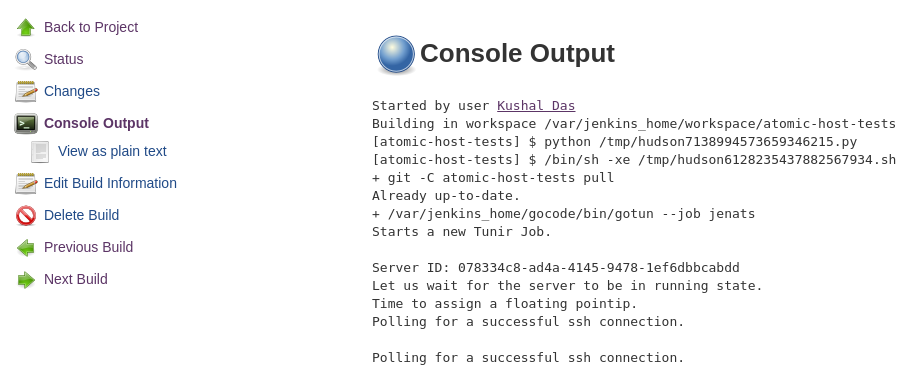
The output from the job.
$ ./gotun --job commands
Starts a new Tunir Job.
Server ID: cb0f491d-a921-46dd-b6e1-3c4353884d6c
Let us wait for the server to be in running state.
Time to assign a floating pointip.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Executing: sudo docker run -d --name redis fedora/redis
Executing: sudo docker run -d --link redis:rd --name client fedora/redis
Executing COPY: scp -o StrictHostKeyChecking=no -r -i /home/kdas/Downloads/kushal-testday.pem ./redistests.py fedora@209.132.184.210:./
Executing: sudo python3 -m unittest redistests.RedisTest.test_set -v
Executing: sudo python3 -m unittest redistests.RedisTest.test_append -v
Executing: sudo docker rm -f client
Executing: sudo python3 -m unittest redistests.RedisTest.test_newclient -v
---------------
Result file at: /tmp/tunirresult_210751937
Job status: true
command: sudo docker run -d --name redis fedora/redis
status:true
Unable to find image 'fedora/redis:latest' locally
Trying to pull repository docker.io/fedora/redis ...
sha256:1bb7b6c03575dd43db6e8e3fc0b06c0b3df0178af9ea382b6f9df577d053bd22: Pulling from docker.io/fedora/redis
a3ed95caeb02: Pull complete
cadab8e68e03: Pull complete
9db1d534feda: Pull complete
a4d5e4eefba6: Pull complete
Digest: sha256:1bb7b6c03575dd43db6e8e3fc0b06c0b3df0178af9ea382b6f9df577d053bd22
Status: Downloaded newer image for docker.io/fedora/redis:latest
b83c3f13fa698627447575651e585f3308e795f579ea772c66d02ae0f1c72939
command: sudo docker run -d --link redis:rd --name client fedora/redis
status:true
6096e414e2f7c314c9601ae6eaedbb3faf9fb265b70a4f77e5ba7b9a93b19209
command: sudo python3 -m unittest redistests.RedisTest.test_set -v
status:true
test_set (redistests.RedisTest) ... ok
----------------------------------------------------------------------
Ran 1 test in 0.199s
OK
command: sudo python3 -m unittest redistests.RedisTest.test_append -v
status:true
test_append (redistests.RedisTest) ... ok
----------------------------------------------------------------------
Ran 1 test in 0.289s
OK
command: sudo docker rm -f client
status:true
client
command: sudo python3 -m unittest redistests.RedisTest.test_newclient -v
status:true
test_newclient (redistests.RedisTest) ... ok
----------------------------------------------------------------------
Ran 1 test in 1.298s
OK
Total Number of Tests:6
Total NonGating Tests:0
Total Failed Non Gating Tests:0
Success.