Testing Fedora MariaDB layered image using gotun
Testing Fedora MariaDB layered image testing using gotun
Yesterday Adam Miller announced the availability of the latest Fedora Layered Image release. The following container images are available in the Fedora registry:
- registry.fedoraproject.org/f25/cockpit:130-1.3.f25docker
- registry.fedoraproject.org/f25/cockpit:130
- registry.fedoraproject.org/f25/cockpit
- registry.fedoraproject.org/f25/kubernetes-node:0.1-3.f25docker
- registry.fedoraproject.org/f25/kubernetes-node:0.1
- registry.fedoraproject.org/f25/kubernetes-node
- registry.fedoraproject.org/f25/mariadb:10.1-2.f25docker
- registry.fedoraproject.org/f25/mariadb:10.1
- registry.fedoraproject.org/f25/mariadb
- registry.fedoraproject.org/f25/kubernetes-apiserver:0.1-3.f25docker
- registry.fedoraproject.org/f25/kubernetes-apiserver:0.1
- registry.fedoraproject.org/f25/kubernetes-apiserver
- registry.fedoraproject.org/f25/kubernetes-master:0.1-5.f25docker
- registry.fedoraproject.org/f25/kubernetes-master:0.1
- registry.fedoraproject.org/f25/kubernetes-master
- registry.fedoraproject.org/f25/flannel:0.1-3.f25docker
- registry.fedoraproject.org/f25/flannel:0.1
- registry.fedoraproject.org/f25/flannel
- registry.fedoraproject.org/f25/kubernetes-proxy:0.1-3.f25docker
- registry.fedoraproject.org/f25/kubernetes-proxy:0.1
- registry.fedoraproject.org/f25/kubernetes-proxy
- registry.fedoraproject.org/f25/etcd:0.1-5.f25docker
- registry.fedoraproject.org/f25/etcd:0.1
- registry.fedoraproject.org/f25/etcd
- registry.fedoraproject.org/f25/toolchain:1-2.f25docker
- registry.fedoraproject.org/f25/toolchain:1
- registry.fedoraproject.org/f25/toolchain
Now, I am going to show how we can add a set of tests for the MariaDB container under gotun on a Fedora Atomic host. I will be firing up the job in the Fedora Infra Cloud.
Because of the nature of the Atomic host, I decided to write a set of tests in golang and build a static binary which can be executed inside of the Atomic host. This way we do not have to worry about any dependency in the host.
$ ldd tunirtests.test
not a dynamic executable
Source code of the test
The following is the source for mysql_test.go.
package main
import (
"testing"
"database/sql"
_ "github.com/go-sql-driver/mysql"
)
func TestMariadb(t *testing.T) {
db, err := sql.Open("mysql", "user:password@/dbname")
if err != nil {
t.Fatal("Can not connect to mariadb", err.Error())
}
defer db.Close()
stmt := "CREATE TABLE IF NOT EXISTS funny (id int(5) NOT NULL AUTO_INCREMENT, name varchar(250), PRIMARY KEY(id))"
_, err = db.Exec(stmt)
if err != nil {
t.Fatal("Can not create table", err.Error())
}
_, err = db.Exec("INSERT INTO funny VALUES (?,?)",1,"kushal")
if err != nil {
t.Fatal("Can not insert data", err.Error())
}
_, err = db.Exec("INSERT INTO funny VALUES (?,?)",2,"Python")
if err != nil {
t.Fatal("Can not insert data", err.Error())
}
rows, err := db.Query("SELECT * from funny")
for rows.Next() {
var uid int
var name string
err := rows.Scan(&uid, &name)
if err != nil {
t.Fatal("Error in selecting data", err.Error())
}
if uid == 1 {
if name != "kushal" {
t.Fatal("Oops, data mismatch", name)
}
}
}
}
As you can see above that I have hardcoded username, password and dub name in the source. This is because while starting the Mariadb container, I can pass those values to the container using environment variables.
I am creating a table, inserting 2 rows in it. Then selecting those rows back to the tool.
the gotun job test file
The following is the content of the mariadb.txt file.
curl -O https://kushal.fedorapeople.org/tunirtests.test
sudo docker run -d --name mariadb_database -e MYSQL_USER=user -e MYSQL_PASSWORD=password -e MYSQL_DATABASE=dbname -p 3306:3306 registry.fedoraproject.org/f25/mariadb
SLEEP 30
chmod +x tunirtests.test
./tunirtests.test -test.run TestMariadb -test.v
At first, I am downloading the binary test file from my Fedora people space. We can also push it to the VM from the host using COPY directive. Next, I am running the docker command to fire up the container with all the required environment variables. After that, I am sleeping for 30 seconds as it takes time to get that container ready for usage. In the last line, I am executing the binary to test the container. Now, we can add more fancy command line arguments to the docker run command (like a data volume), and then test those too. But, I am going to keep those as an exercise for the reader :)
If you have any comment, feel free to drop me a mail, or tweet to @kushaldas.
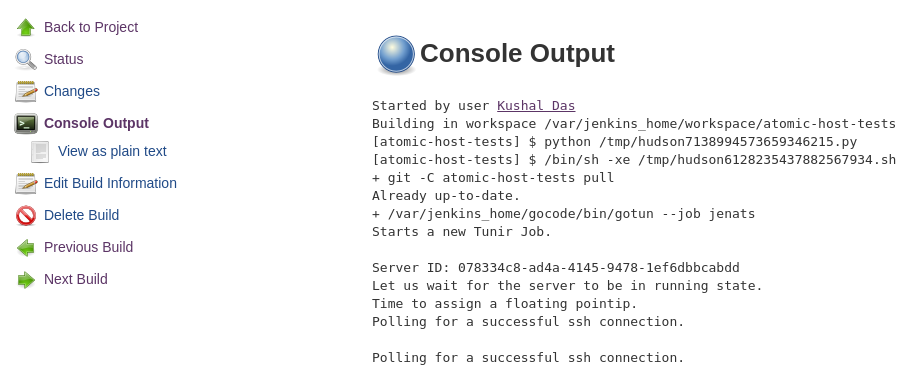
The final output from the test is also given below.
./gotun --job mariadb
Starts a new Tunir Job.
Server ID: 9c4168ae-d8c4-4534-a53c-c2a291d4f6c5
Let us wait for the server to be in running state.
Time to assign a floating pointip.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Polling for a successful ssh connection.
Executing: curl -O https://kushal.fedorapeople.org/tunirtests.test
Executing: sudo docker run -d --name mariadb_database -e MYSQL_USER=user -e MYSQL_PASSWORD=password -e MYSQL_DATABASE=dbname -p 3306:3306 registry.fedoraproject.org/f25/mariadb
Sleeping for 30
Executing: chmod +x tunirtests.test
Executing: ./tunirtests.test -test.run TestMariadb -test.v
---------------
Result file at: /tmp/tunirresult_586858839
Job status: true
command: curl -O https://kushal.fedorapeople.org/tunirtests.test
status:true
%!T(MISSING)otal %!R(MISSING)eceived %!X(MISSING)ferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 4347k 100 4347k 0 0 3722k 0 0:00:01 0:00:01 --:--:-- 3725k
command: sudo docker run -d --name mariadb_database -e MYSQL_USER=user -e MYSQL_PASSWORD=password -e MYSQL_DATABASE=dbname -p 3306:3306 registry.fedoraproject.org/f25/mariadb
status:true
Unable to find image 'registry.fedoraproject.org/f25/mariadb:latest' locally
Trying to pull repository registry.fedoraproject.org/f25/mariadb ...
sha256:9a2c3bc162b6b1a1c286302c3e635d77c6e31cbca5d354ed0a839c659e1ecfdc: Pulling from registry.fedoraproject.org/f25/mariadb
be44cf43edd1: Pull complete
a87762b3425a: Pull complete
Digest: sha256:9a2c3bc162b6b1a1c286302c3e635d77c6e31cbca5d354ed0a839c659e1ecfdc
Status: Downloaded newer image for registry.fedoraproject.org/f25/mariadb:latest
e9c72f1f41b1ec763418f969359c3319bdc4c95d8123fc3b5e6617768b90d00f
command: chmod +x tunirtests.test
status:true
command: ./tunirtests.test -test.run TestMariadb -test.v
status:true
=== RUN TestMariadbConnect
--- PASS: TestMariadbConnect (0.20s)
PASS
Total Number of Tests:4
Total NonGating Tests:0
Total Failed Non Gating Tests:0
Success.